Is your organisation taking advantage of the benefits of cloud computing? And if so, do you understand the responsibilities that come with securing your environment? These are big questions for many organisations in the modern workplace. In this post we will take a dive into the current state of cloud adoption, and the framework – called the Shared Responsibility Model – which helps organisations understand their obligations in ensuring the security of their data and assets in the cloud.
The Current State of Cloud
Cloud computing is far from a new concept, with the term itself attributed by many to Google’s then CEO Eric Schmidt in an August 2006 industry conference. Since that time, it has become a part of the business vernacular, with increasing adoption year on year.
In simple terms, “the cloud” is an all-encompassing term that applies to the space on shared servers hosted by third parties that businesses can rent. It acts as an alternative to the more expensive and demanding solution of organisations owning and maintaining a physical infrastructure on-premise. There are many benefits to moving your organisation to the cloud. Among these are potentially reduced IT infrastructure and operating costs as well as access to far greater economies of scale.
But if it’s all about benefits to a business, why are there many yet to take the plunge? The reluctance of some organisations is largely based on concerns around security. According to LogicMonitor’s Cloud Vision 2020: The Future of the Cloud report, 66 per cent of IT professionals say that security is their primary concern in adopting an enterprise cloud computing strategy. 60 per cent also highlighted fears around governance and compliance as being a key factor.
This perception of greater security risk has led some organisations to delay a migration to cloud, but the reality is that the cloud itself shouldn’t be any less secure than your on premise infrastructure – the primary issue is a lack of understanding of how to employ best practice. Indeed, the security features available to you in the cloud can actually provide greater security than on-premise, assuming they are effectively utilised. This is where understanding the Shared Responsibility Model is vital. Whether your organisation has already moved to a cloud or hybrid environment, or is currently contemplating the change, it is critical that you understand your responsibilities when it comes to cloud security.
As Jay Heiser, Vice President Analyst of Gartner once said: CIOs must change their line of questioning from “Is the cloud secure?” to “Am I using the cloud securely?”
What is the Shared Responsibility Model?
The Shared Responsibility Model is a globally accepted cloud security framework that reflects the security obligations and responsibilities of your cloud provider and those that belong to you, the customer.
While the responsibilities are clearly outlined in the model, there is some persistent misunderstanding of the line in the sand – perhaps defined as simply as “security of the cloud” and “security in the cloud”. More on that in a moment. Historically speaking organisations who maintained everything in an on-premise datacentre would have effectively held responsibility for all aspects of their security, both physical and virtual.
Now that the infrastructure has moved to a third-party cloud provider – AWS or Azure for example – they hold responsibility for ensuring that the infrastructure is secure. Meanwhile, you the customer are responsible for everything from assets and data to apps that sit within the cloud environment.
It is also important to consider which cloud workloads or services you are utilising, as there are key differences in responsibility ownership within the model.
What are the different workloads?
- Infrastructure as a Service (IaaS): provides organisations with access to physical or virtual servers, networking and storage
- Platform as a Service (PaaS): provides organisations with access to operating systems and software to develop applications
- Software as a Service (SaaS): provides users with access to specific applications as a service via web or app
The following diagram from Microsoft illustrates your areas of responsibility across all workloads (SaaS, IaaS, PaaS and on-premise).
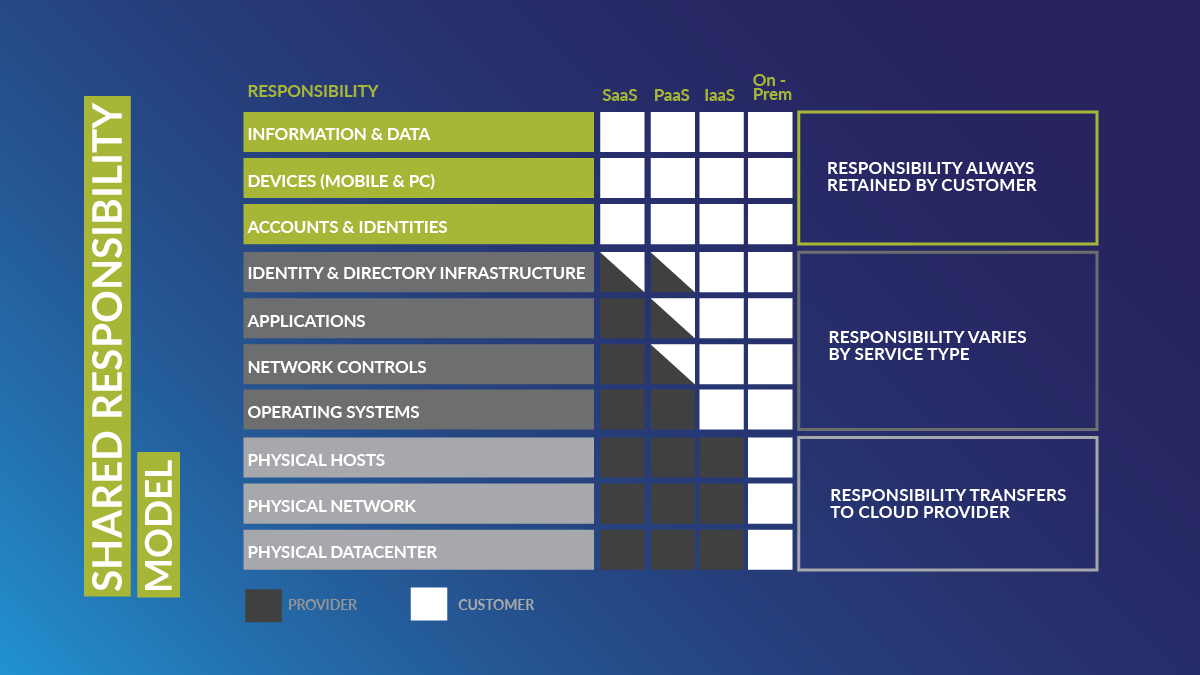
While there are some areas where responsibility changes depending on your service type, there are some defined rules:
- For all cloud workloads your service provider manages the physical aspects – hosts, networks and datacentres
- For all cloud workloads you own responsibility for your data, endpoints, accounts, identities, and access management
Why is the Shared Responsibility Model Important?
According to Gartner’s latest forecast, “through 2025, 99 per cent of cloud security failures will be the customer’s fault”. Whilst that is an alarming projection, it does tell us that organisations that are already in the cloud or are moving to it must absolutely understand their responsibilities if they want to benefit from the cloud securely.
So, let’s have a quick look at some of the major risks associated with your areas of responsibility. We now know that the cloud provider is doing their part to secure your infrastructure, and that’s great news. But what is going on inside your cloud environment?
Compromised Privileged and non-Privileged Accounts
One major risk area that sits within your responsibility is identity and access management. Do you have strong authentication mechanisms in place? More importantly, do you know if any of your users have already been breached? Forrester Research estimates that “at least 80 percent of data breaches have a connection to compromised privileged credentials.”
Furthermore, while privileged accounts are the greater risk and higher reward target for cyber attackers, you should not neglect lower privileged accounts given that identities are now your new security perimeter.
Shadow IT
Do you have oversight of shadow IT, i.e. corporate users accessing non-approved SaaS applications? Estimates on unsanctioned cloud app usage in organisations fluctuate from the hundreds to the thousands, and the reality is that unless you already have adequate controls in place, you may not even be aware of the risk.
A basic premise that applies here is that you can’t secure what you can’t see. Given Gartner’s view that a third of successful attacks experienced by enterprises will be on their Shadow IT resources during 2020, a lack of visibility is not a risk you will want to take.
Unprotected Sensitive Data
Another question to ask: how certain are you that important documents and sensitive data are appropriately protected? It is not uncommon for organisations with a high usage of cloud apps among employees to find that sensitive documents have inadvertently been made accessible to the public or would-be attackers. You would be surprised how many organisations have simply assumed that this is all taken care of and under the responsibility of their cloud provider. Research carried out by Skyhigh showed that 21% of files that were uploaded to cloud-based file-sharing apps contained sensitive data, including intellectual property.
These risks highlight only some of the reasons why adhering to best practice, understanding the Shared Responsibility Model, and applying adequate controls in whatever cloud environment you use are critical.
All you need to do is look at the morning news to see how costly a data breach can be for your organisation. You run the risk of reputational and brand damage, loss of income or business, and then the sanctions and fines that come from contravening GDPR in the EU and many other directives. It’s simply not a risk worth taking.
Securing Your Network
Do you have oversight of all traffic flowing through your network? While network security is often considered a more traditional pillar of your security stack – and a critical one at that – moving your infrastructure to the cloud doesn’t change its importance. The key difference is that the way you manage network security from the cloud requires a different approach. Moving machines and workloads from your on-premise environment requires that you consider aspects to your network security such as Network Security Groups (NSGs), Application Firewalls, and Just In Time (JIT) Administration Controls.
Increasingly Sophisticated Threats
Phishing and malware continue to be the top threat vectors to an organisation’s security, regardless of whether you are in the cloud or on-premise. It is essential that you rigorously monitor and defend against attacks no matter your environment. Fundamental basics such as timely patch management and network access controls are equally essential whether protecting on premise, hybrid or cloud infrastructure.
Fortunately, keeping on top of threats and identifying if you are at risk can be easier when using cloud services. This is largely due to the extensive datasets that many cloud-based solutions can provide access to, giving you insight into global threats that other organisations have faced. Additionally, many of these tools utilise machine learning and AI to understand whether your workstations and servers are potentially at risk. This means that your administrators can gain visibility into which resources they should focus on as well as what they need to do to mitigate the risk.
How Can Your Organisation Stay Secure in the Cloud?
The biggest challenge for organisations is understanding and applying the Shared Responsibility Model to their own environments – and this can feel quite daunting. However, there are a range of solutions that can help organisations gain visibility, take back control and proactively defend against threats.
Understanding what elements sit under your responsibility within the model is just the first step. Now you need to get a clearer picture of your environment and take proactive steps to continually improve your security posture. Engaging with experienced consultants and undergoing a cloud security assessment is an excellent next step on your way to understanding your security baseline and building a roadmap to help your organisation stay on top of security while on your journey to digital transformation.
Ready to secure your digital transformation journey with Microsoft Security?
Threatscape are one of very few specialised security companies with a dedicated Microsoft Security Practice. Our expertise in this space is reflected in our status as a Gold Partner and the global Microsoft Security & Compliance Partner of the Year for 2020/21. Our consultants work exclusively with Microsoft Security solutions to provide a range of managed and professional services.
Threatscape are pleased to offer the next generation of security posture management. Overwatch for M365 Security is a continual optimisation service that offers your organisation access to award-winning Microsoft security expertise across the entire M365 platform.