Try as we might, it’s impossible to guard against all cyber attacks, all the time. Cyber criminals are committed, well-resourced and increasingly sophisticated. It’s inevitable that some intrusions will slip through the cracks.
Whatever your security posture, whether through a zero-day exploit, misconfiguration or human error, threat events can be beyond your control. But what you can control is your preparedness, your detection, and your response.
How? Through continuous security optimisation, effective training, and an established response plan. In short, by getting Left of Bang.
What is Left of Bang?
The phrase Left of Bang was coined by Jason A. Riley and Patrick Van to describe a tactical military approach used to limit the loss of life.
On an attack timeline, the impact, or Bang, is in the centre. Everything to the Left of Bang precedes the attack, and everything to the Right of Bang immediately follows it.
Situating yourself Left of Bang directs your attention to preparation, rather than response. From here, you can:
- Assess your environment
- Anticipate and mitigate incoming attacks
- Craft a robust response plan to limit impact
- Jump to action when a threat is identified
What's The Connection Between Left of Bang and Cyber Security?
Beyond its military origins, Left of Bang is a useful lens through which to view cyber security. With the best will and security solutions in the world, you can never prevent all attacks. By accepting this unfortunate reality and focusing organisational attention on the Left of Bang (the lead-up to impact), an attack’s business impact can be minimised.
In cyber security terms, Left of Bang refers to proactive organisational measures taken to prepare for incoming attacks. Namely: planning, training, and continuous proactive security optimisation.

Planning
As the adage goes, fail to plan… Many organisations focus on the tools required to avoid cyber attacks, neglecting to consider what will happen if (and when) they do. This lack of planning inevitably leads to delays in the identification of threats, poor communication regarding threat procedures, and ultimately greater business impact.
While no single threat response plan can cater to every eventuality, establishing a framework to which all staff can adhere will save time at a crucial moment and lead to decisions made on data, rather than emotion.
As well as creating a threat response plan, regular testing and simulations should be scheduled to measure prospective organisational response, disaster recovery and business continuity.
Training
Talent resourcing is a growing threat in the cyber security industry. When teams are spread thin, little time is available for the continuous upskilling and training required to keep abreast of developing security technologies.
Organisations unable to dedicate the necessary time and budget to training their existing team (or outsourcing unmanageable duties to external providers) risk falling Right of Bang.
Security solutions and threat actors are constantly evolving. Regular practical training on your stack’s functionalities and vulnerabilities is essential for keeping your organisation prepared for emerging threats, and crucially, Left of Bang.
Cyber Security Optimisation
Security optimisation is the key to staying Left of Bang, and should underpin your entire security strategy.
Security optimisation is a continuous process of identification, evaluation, and improvement to maintain and strengthen your security posture. Rather than viewing security optimisation as a means to an end, consider the process a never-ending strategic approach to ensuring security best practice.
Ultimately, the primary goal of security optimisation is to reduce the likelihood of a successful attack.

What is Cyber Security Optimisation?
Security optimisation takes a holistic appraisal of your security posture to assess its components, evaluate its weaknesses and provide a proactive roadmap for the future.
It can be broken down into three key stages…
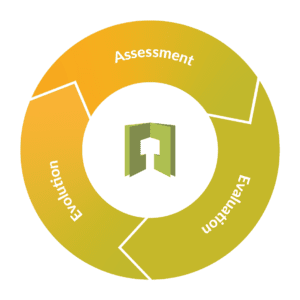
Assessment
Begin your security optimisation journey by getting a bird’s eye view of your entire posture. This can be intimidating for organisations with a sprawling stack of solutions, but thorough visibility is essential.
This stage of security optimisation should focus on:
- Retrieving historic and current data for benchmarking and analysis
- Identifying gaps (or overlaps) in your stack
- Checking the application of existing tools, and whether they’re being used effectively
- Ensuring configurations are current and updates are applied
Evaluation
The intelligence gathered through assessment of your security posture should now be used to evaluate your stack’s depth, strength, and potential for improvement.
Consider:
Training Requirements & Your Response Plan
Security optimisation complements training and planning and should be implemented in tandem for maximum effectiveness.
Your Range of Security Solutions
Many organisations find that rather than needing more solutions to bridge gaps between tools, they are in fact oversubscribed to a selection of disparate tools that don’t work harmoniously. If assessment proves difficult and threat data isn’t cohesive, this may be a sign that your posture is too complex to be effectively implemented and managed.
Patching Vulnerabilities
Over 40 percent of breaches can be attributed to gaps in patching, where despite a patch being available for a known vulnerability, it isn’t applied. Without the resources to adequately manage patching, the capabilities of security tools are not leveraged, and businesses remain vulnerable despite security investment.
Permissions and Access
Privilege creep opens the door to internal threats and poses a significant risk to information security. Use this opportunity to ensure user permissions accurately reflect current roles.
Cyber Attack Surface
As attack vectors increase through growth, all new technologies should be cohesively built into cyber security strategy. If organisational scaling and user requirements (particularly in terms of remote working and cloud-based applications) have outstripped the capabilities of your existing security team, new vulnerabilities can go unchecked.
ROI
When solutions’ functionality overlaps and individual threat reduction can’t be demonstrated, accurately measuring ROI becomes a minefield. Utilise security optimisation to identify where value of investment isn’t being realised.
Threat Identification
With the data amassed during the assessment phase, evaluate the effectiveness of your organisation’s threat identification, and subsequent procedures, from first alert through to remediation.
Risk Tolerance
The recurring cycle of optimisation offers a chance to reassess organisational risk tolerance and how developments in your security posture impact established risk vectors.
Evolution
Before beginning the cycle again, the final stage of security optimisation is concerned with security evolution. Armed with greater visibility, prioritisation of security resources is better informed and based on meaningful data. This shift in approach to business security positions your team Left of Bang.

What Are the Benefits of Security Optimisation?
With a robust plan of security optimisation, organisations can expect to achieve:
Increased Visibility and Insight
At the core of preparedness (and staying Left of Bang) is comprehensive, reliable, useful data, as emphasised by Gartner –
“Whether it’s gathered from business reports, benchmarking, current state assessment or asset inventory, data is critical… Data can be used to move away from making decisions based on legacy or emotions, and toward efficiency and metrics. It will enable you to showcase and highlight how security and risk is making decisions and why you’ve reached a particular conclusion.”
Commitment to continuous security optimisation ensures data remains at the fore of security strategy and is used to inform decision making from security teams up to the C-suite.
Improved Detection
From identifying potential vulnerabilities and misconfigurations to spotting incoming attacks, the quicker the detection, the lower the likelihood of a damaging business impact.
Security optimisation empowers teams to proactively implement effective detection and response procedures. According to 2022 research Cybersecurity Solutions for a Riskier World, it takes organisations 128 days detect a breach on average. But with a complete picture of your security posture (and a streamlined suite of solutions), detection and resolution needn’t feel like searching for a needle in a haystack.
Measurable ROI
By keeping on top of your security stack through continuous assessment and evaluation, solutions that have been outgrown, or are no longer effectively utilised, can be confidently trimmed from your catalogue without the threat of unknown impact. This streamlining of security products simplifies the task of measuring ROI by minimising dashboards and reports into a manageable, consolidated pool of essential platforms and tools.

Ongoing security optimisation, wherever possible, is key to strengthening security posture and maximising ROI for all organisations. It’s at the very core of a Left of Bang approach to cyber attacks.
But in the long term it’s important to be realistic about your team’s capabilities and resources. Remember…
- Many attacks occur during down-time – hackers in the infamous 2016 Bangladesh Banking heist exploited weekends and national holidays in the hope of escaping detection. Are you able to monitor and respond to threats in the middle of the night, or on Bank Holidays?
- Security vendors deploy updates and functionality changes in real-time, creating a dynamic and fluid environment. Are you able to track these changes and amend your configurations as necessary across your entire security stack?
- As technologies develop at a whirlwind pace, vendors have responded with a wealth of often disparate solutions. Are you able to keep on top of your security stack?
- In a cloud-based world, changes are continuous. Last week’s best practice is outdated by Monday morning. Are you able to maintain stringent security standards at pace?
If the answer is no, your organisation may benefit from an external management service to complement your team and strengthen your existing security stack with improved coverage.
Your Route to Security Optimisation
For organisations utilising the M365 Security platform, Threatscape’s own Overwatch service offers the next generation of security posture management. With Overwatch, M365 security optimisation is driven by our award-winning Microsoft Security Practice consultants, with evolving strategy tailored to your environment.
Providing an initial assessment followed by monthly workshops to deliver guidance and assistance in driving constant security optimisation, governance, and compliance for the business, Overwatch for M365 simplifies security without compromise.





![[M365 AI] Copilot & AI Agents: Tips You Must Know](https://www.threatscape.com/wp-content/uploads/2025/07/COPILOT-PODCAST-3-300x169.jpg)



