What is the CIA triad?
The CIA triad is a cyber security—and specifically information security—model designed to inform and maintain an organisation’s security policies to identify vulnerabilities and continue strong practices.
Developed over time to address ongoing cyber security needs, the model remains a significant framework today, used in ISO 27001, a globally recognised standard for information security, as well as within Article 32 of the GDPR, which outlines geographically-impacted organisations’ obligation to employ appropriate measures to protect and maintain their stored data and information.
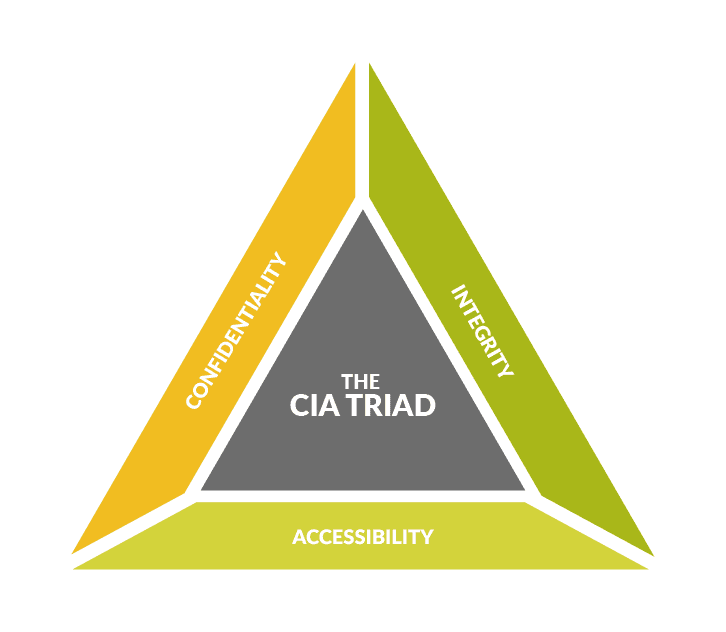
Not to be confused with the Central Intelligence Agency, in this context, CIA stands for: confidentiality, integrity, and availability.
Each element can be understood as follows:
Confidentiality
Within the CIA triad confidentiality refers to the limits set upon access to information, similar to what we might commonly understand as privacy. These measures are designed to keep sensitive data safe from unauthorised access attempts, as well as from being divulged (intentionally or accidentally) to those without the necessary clearance. By properly understanding the differing business impact of potential data breaches, confidentiality can be attributed accordingly, and measures can be implemented to keep the most sensitive data safe with the highest priority.
Integrity
Integrity refers to the accuracy, consistency, and trustworthiness of an organisation’s data throughout its lifecycle, from creation through to destruction, with a reliable audit trail as required. A major concern regarding the integrity of data is ensuring that it is not modified during its lifecycle by those without authorisation, and so the CIA framework seeks to prioritise the proper storage of data, so that it might exit an organisation exactly as it entered, except in the case of agreed, appropriate, and catalogued changes performed internally.
Availability
A crucial element for audit and compliance, availability speaks to data and information being easily, reliably, and consistently accessible to those parties authorised to view and/or modify it. Regardless of whether data is both confidential and kept to a strict integrity, if it cannot be accessed at will, there may be gaps in security. To ensure availability, associated hardware and infrastructure should be maintained as a priority, with practical use cases at front of mind.

Why is the CIA triad important for cyber security?
Within information security confidentiality, integrity, and availability are paramount. Whether or not an organisation chooses to utilise the CIA triad framework as a means to achieving reliably secure information security practices, these are considerations that all businesses should have at the fore to ensure data is being handled sensitively, securely, and in accordance with relevant compliance and regulatory requirements.
The CIA triad is also a useful lens through which to view ongoing cyber security optimisation, categorising continuous housekeeping tasks into their relevant areas to make the task manageable and effective.
It can also be utilised when adopting new technologies and solutions, prompting an analysis of where value is being added by new investments in these three core areas of information security, as well as whether new tools will be able to work cohesively with existing products to maintain an organisation’s data security.
How does the CIA triad work in unison?
When displayed visually, the CIA triad is represented as a triangle, with confidentiality, integrity, and availability at each vertex. There’s a reason for this.
When working with the triad, each element should be considered in relation to the others, with equal importance, and simultaneously. It’s not a case of addressing one area with greater priority than the others, rather, organisations should consider all three facets together when implementing or maintaining their information security practices.
In practice, this means that while a new security solution might benefit an organisation’s data confidentiality, if it also hinders the same data’s availability, more consideration should be given to how the new solution truly benefits security as a whole. An example of this might be implementing new MFA practices. While this undoubtedly improves confidentiality and limits unintended access, if the MFA process is not a smooth, reliable, intuitive one, the accessibility and in turn availability of data is impacted, which might see users searching for less secure workarounds.
Thinking of the CIA triad’s three elements as an interconnected system working towards holistic data security will help organisations to understand the relationship between the three and get the most from the model.
Threatscape offers a wide variety of professional services purpose-built to address businesses evolving cyber and information security needs. Whether that’s upskilling your internal team, deploying a new solution, ongoing technical support, or an industry-specific security challenge, we have the capability to support your business.
Talk to us today and an account manager will be in touch to advise how we can best support your cyber security journey.





![[M365 AI] Copilot & AI Agents: Tips You Must Know](https://www.threatscape.com/wp-content/uploads/2025/07/COPILOT-PODCAST-3-300x169.jpg)



